Security Services
Delivering Quality Security Services Our Client’s Rely On
Security Services
Our team of industry experts provides complete security services, including assessment, design, preparation, management, installation, and support for projects of any size or location. Unlike some integrators who focus only on the sale, CGL Electronic Security prioritizes selecting, designing, and installing systems that protect our clients’ most valued assets today and in the future. Since 1998, we have worked closely with clients to plan, design, install, support, and maintain security systems regionally, nationally, and globally.

Global Reach
Controlling doors and monitoring video surveillance systems at any location may seem impossible, but our clients do it every day. Since our founding, CGL Electronic Security has deployed systems that let clients track their operations across the globe.
CGL proudly participates in the PSA Security Network, the world’s largest systems integrator cooperative. Partnering with PSA Network members and system manufacturers allows us to act as a single point of contact. We coordinate and direct security integration at client facilities worldwide, giving clients peace of mind both locally and globally.

Managed Security Services
Not every organization, business, or school needs an on-premise access control system or has the resources to manage it. CGL’s managed and hosted access control systems look and operate like an on-premise system but require no in-house administration.
We install card readers, door hardware, and other security devices to meet each client’s access control needs. After installation, our managed access experts configure the system and distribute access cards, fobs, or biometric and mobile credentials. This allows clients to focus on their business while we manage the security system.
Project Management
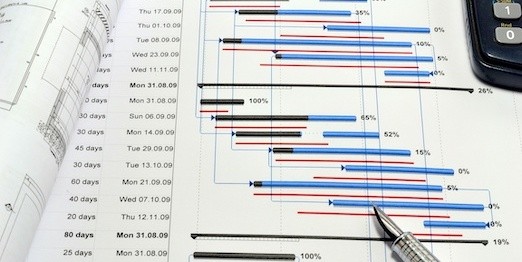
CGL’s project management process begins with information gathered by Account Managers, Engineers, and Project Managers to create a clear plan and schedule. During each project, our installation team—including Project Managers, Lead Technicians, and Apprentice Technicians—tracks progress to ensure accuracy and client satisfaction.
We digitize site surveys and system designs to avoid missing any details. Unlike competitors, we provide every client with full CAD drawings, including wiring details for all panels.

System Design
After completing a vulnerability assessment, the CGL team works closely with clients to identify weaknesses to address during system design. Each client has unique needs, and our designs reflect their specific security and safety requirements.
Our system design process may update existing systems, integrate multiple security systems, or create entirely new ones. Whatever your needs, we deliver a system that protects your most valued assets on time and within budget.

Security System Support
CGL knows clients value reaching a friendly, professional voice by phone or receiving a timely email response. Our account managers oversee each project from day one, understanding client requirements and supervising the entire design and installation process.
Our disciplined and organized team of account managers, support personnel, field technicians, and project managers maintains constant communication to ensure systems operate as intended. If issues arise, our skilled and certified technicians quickly resolve them.

Vulnerability Assessments
Our experience as security professionals has taught us that no two clients are alike. We avoid “one size fits all” solutions, which is why CGL conducts tailored security vulnerability assessments for hundreds of clients across New England.
We work with clients to identify their most valued assets, understand potential threats, and evaluate business interruption risks. Using this information, we develop practical protection plans. The CGL security vulnerability assessment is a critical first step toward a comprehensive electronic security system designed to mitigate risk.
